Google discloses Windows bug as Microsoft objects
Google published the bug after only seven days because ‘we know it is being actively exploited’
Google late on Monday released details of a serious flaw in Windows against the objections of Microsoft, which argued the disclosure puts users at risk since there is currently no fix available.
The search company regularly releases bug reports through its controversial security programme, which has a policy to disclose flaws on a set schedule whether they have been fixed or not.
The policy is intended to put pressure on software makers to make fixes available faster. In most cases Google waits 60 days before disclosure, but when a bug is known to be actively exploited to attack systems – as in this instance – the period drops to seven days.
 “After seven days, per our published policy for actively exploited critical vulnerabilities, we are today disclosing the existence of a remaining critical vulnerability in Windows for which no advisory or fix has yet been released,” Google said. “This vulnerability is particularly serious because we know it is being actively exploited.”
“After seven days, per our published policy for actively exploited critical vulnerabilities, we are today disclosing the existence of a remaining critical vulnerability in Windows for which no advisory or fix has yet been released,” Google said. “This vulnerability is particularly serious because we know it is being actively exploited.”
Google explained that the bug allows remote attackers who have access to a low-level account to execute code with higher-level privileges, allowing them to bypass a security sandbox and do more damage.
An attack can be triggered using a particular win32k.sys system call, detailed by Google in its advisory. The company said its own Chrome browser blocks such calls using the Win32k lock-down mitigation feature in Windows 10.
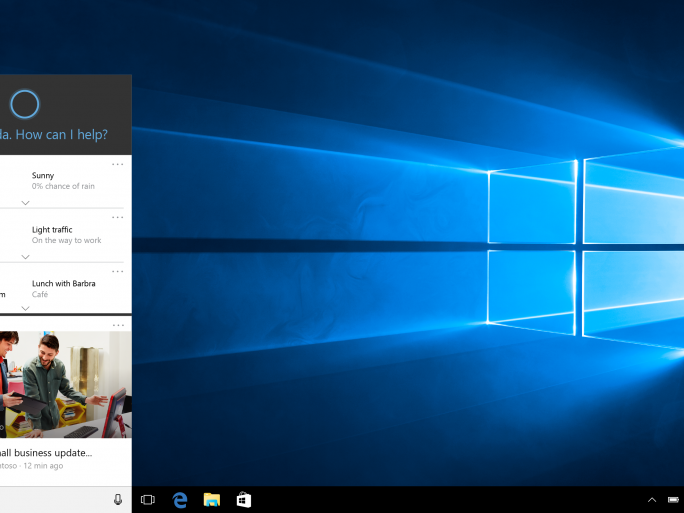
Microsoft said the disclosure could expose customers to danger: “Today’s disclosure by Google could put customers at potential risk. We recommend customers use Windows 10 and the Microsoft Edge browser for the best protection.”
 Last year Google said it would give software vendors extensions to its 60-day disclosure period if they say they’re working on a patch, but that doesn’t apply to bugs being actively exploited, which get only seven days.
Last year Google said it would give software vendors extensions to its 60-day disclosure period if they say they’re working on a patch, but that doesn’t apply to bugs being actively exploited, which get only seven days.
“Seven days is an aggressive timeline and may be too short for some vendors to update their products, but it should be enough time to publish advice about possible mitigations, such as temporarily disabling a service, restricting access, or contacting the vendor for more information,” Google says in its policy statement.
“As a result, after seven days have elapsed without a patch or advisory, we will support researchers making details available so that users can take steps to protect themselves.”
Google also disclosed a bug in Adobe’s Flash Player that it had reported to Adobe on 21 October, the same day it informed Microsoft of the Windows flaw. Adobe fixed the bug, identified as CVE-2016-7855, in a 26 October update, Google said.
“We encourage users to verify that auto-updaters have already updated Flash — and to manually update if not — and to apply Windows patches from Microsoft when they become available for the Windows vulnerability,” Google noted.